5 ways to protect yourself safe from cyber-attacks and ransomware.
By Dennis Shelly
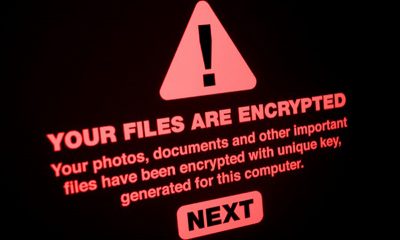
After a major cyber-attack involving ransomware, top US fuel pipeline provider Colonial Pipeline shut down its entire network, affecting approximately half of the US East Coast’s fuel supply. The event is one of the most significant digital ransom operations ever recorded, and it has highlighted the vulnerability of the United States’ energy infrastructure to hackers. If the line is shut down for an extended period of time, costs at gas stations will rise ahead of the peak summer travel season, causing a possible economic and market blow to the United States. According to Digital Shadows, the coronavirus pandemic aided the Colonial attack having more engineers remotely access pipeline control systems from home.
The ransomware attack was carried out by a group of cybercriminals known as Darkside, who hacked into a company’s or government’s network and scrambled the data. After that, the hacker leaves a message in the system demanding payment. If the company pays up, the hacker relinquishes control. Experts warn that ransomware attacks – which are part-ransom, part-blackmail, and part-invocation of squatters’ rights – are becoming more common and that the mainly Russian-based hackers’ methods are becoming more sophisticated. According to Emsisoft, nearly 2,400 government agencies, health care services, and schools in the United States were victims of ransomware attacks in 2020. Although this number is likely an undercount because many victims are unable to report break-ins in the first place. According to a recent report, the subsequent economic hit is huge, with figures ranging from $57 billion to $109 billion annually.
How to stay safe – 5 ways to protect yourself safe from cyber-attacks and ransomware.
Experts recommend the following steps to defend your company from ransomware:
- Prohibit unnecessary connections to remote desktop services (such as RDP) over public networks, and make sure to use secure passwords for these services. Install all patches for VPN solutions you use to connect remote staff to the corporate network.
- Using public Wi-Fi networks with caution is a good way to defend yourself from ransomware. Your computer is more vulnerable to attacks when connected to a public Wi-Fi network. Avoid using public Wi-Fi for confidential transactions or use a secure VPN provider to remain safe.
- To avoid exploiting vulnerabilities, update all software on all connected devices. Updating your applications and operating systems regularly helps to keep you safe from ransomware. Make sure you’re using the most recent security patches as you update. This makes it more difficult for cybercriminals to exploit vulnerabilities in the applications.
- Back up your data on a daily basis to ensure that you have ready access to the backups in case of an emergency. Utilize threat intelligence data to remain current on attack tactics, techniques, and procedures. Use security solutions to help prevent attacks from occurring in the first place. Concentrate the defense strategy on detecting lateral movement and data exfiltration, with a particular focus on all outbound traffic.
- Ransomware can also infect your computer via email attachments. Any attachments that seem to be suspect should be avoided. Pay close attention to the source and double-check that the address is right to ensure that the email is trustworthy. You can never open attachments that require you to run macros to view them. If the attachment is infected, opening it will activate a malicious macro that will enable malware to take control of your computer. Use a reliable endpoint protection solution that detects and counters exploits, as well as the ability to roll back malicious changes and restore the system.
It’s necessary to use a technology like zero trust, which restricts access to critical systems. Any major infrastructure prprovider from energy to transportation to water systems and healthcare and more—should be equipped or retrofitted with zero trust security controls that also allow workers and contractors to do their work more safely, and that provide far greater safety to vital infrastructure. Zero trust network access solutions are a good place to start as they limit access to only the applications that an employee or contractor requires to do their job.
Wrap Up
 The implementation of the above tips should help provide the majority of users with adequate protection from ransomware. Regardless of what precautions you take to secure your records, the use of common sense is always your best option. If something doesn’t look right, it usually isn’t. Stay updated with apps, use anti-malware software, stop accessing files and applications from unknown places or strangers, and make sure that your backup is up to date.
The implementation of the above tips should help provide the majority of users with adequate protection from ransomware. Regardless of what precautions you take to secure your records, the use of common sense is always your best option. If something doesn’t look right, it usually isn’t. Stay updated with apps, use anti-malware software, stop accessing files and applications from unknown places or strangers, and make sure that your backup is up to date.
Our Cyber Security Eggsperts are ready to help with protecting you and your business from the threats of cybercriminals and ransomware.
Contact one of our Cyber Security Eggsperts today! We are ready to help with a complete cybersecurity solution for you, your business, and your home today, by calling (760) 205-0105 or emailing us with your questions, service requests, or even just to chat.
IT | Networks | Security | Phones | A/V | Integration